boberdoo Trust Center
Doing what's right since 2000

SOC 2 Audited
SOC 2 Type II
Our Guiding Principles
Protect Data as a Valuable Asset
We believe that data is a valuable asset and should be protected accordingly for confidentiality, integrity and availability of the data under our care.
Embrace Best Practices
We embrace best practices, industry standards and evolving regulations because we believe they make us, and our industry, better.
Exceed Expectations
We adapt our business to meet and exceed the security and privacy expectations of our clients and partners.
Promote Awareness
We promote security awareness and transparency among our employees, consumers and industry partners.
Continuous Improvement
We pursue continuous improvement in security and privacy practices to protect our employees, clients and consumers against evolving threats.
Enable Data Retention Policies
We encourage and enable clients to implement robust data retention and deletion policies because we believe that lead companies should retain data only as long as required to provide the requested service to consenting consumers — not forever.
Information Security Program Overview
A Comprehensive Approach to Security
boberdoo.com LLC has developed and maintains a comprehensive information security program committed to protecting the confidentiality, integrity and availability of boberdoo systems and data. We strive to provide assurance of compliance with our internal policies, internationally recognized best practices and external regulatory requirements.
Key Components of our information security program include:
• Our Guiding Principles
• Framework (based on NIST CSF)
• Security Organization
• Trusted Security Partners
• Policies, Procedures and Standards
• Risk Management Practices
• Security Awareness Training
• Network Protection
• Technical Security Controls
• Access Management
• Vulnerability Management
• Logging and Monitoring
• Incident Response
• Disaster Recovery
• Application Security (Lead System Security Features)
boberdoo conducts a self-assessment against the MVSP (Minimum Viable Secure Product) checklist at least annually and uses data seeding processes using Assumed Seeds. Minimum Viable Secure Product (MVSP) is a list of essential application security controls that should be implemented in enterprise-ready products and services. The controls are designed to be simple to implement and provide a good foundation for building secure and resilient systems and services. MVSP is based on the experience of contributors in enterprise application security and has been built with contributions from a range of companies.
Key Components
- Guiding Principles
- Framework (NIST CSF)
- Security Organization
- Trusted Security Partners
- Policies, Procedures & Standards
- Risk Management
- Security Awareness Training
- Network Protection
- Technical Security Controls
- Access Management
- Vulnerability Management
- Logging and Monitoring
- Incident Response
- Disaster Recovery
- Application Security
Security & Compliance Framework
NIST Cybersecurity Framework
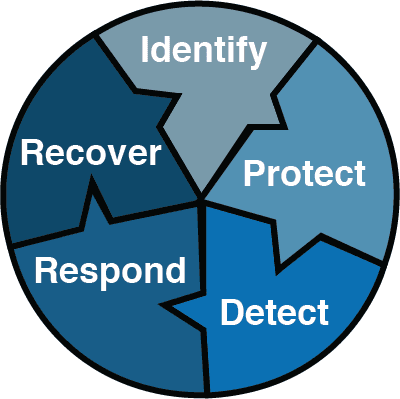
We have adopted the NIST Cybersecurity Framework, which is a voluntary framework consisting of standards, guidelines, and best practices to manage information security risk. Our framework helps to guide us in protecting the confidentiality, integrity and availability of boberdoo infrastructure, systems, applications and data. Our policies, procedures and standards follow best practices and controls derived from NIST, ISO 27001, CIS-AWS Benchmarks, CIS Critical Security Controls, HIPAA, PCI DSS, GDPR and other industry standards and regulations.
IDENTIFY
Security Organization
The Information Security program is organized around and developed by our Chief Information Security Officer (CISO) and supported by company ownership/leadership and operational subject matter experts. boberdoo personnel maintain industry-recognized certifications including Certified Information Systems Security Professional (CISSP), ITIL, AWS certifications and others.
Policies, Procedures and Standards
boberdoo has developed policies and procedures and adopted standards intended to support our compliance with internationally recognized best practices and regulatory requirements. Our information security policies address network protection, systems monitoring & logging, endpoint protection, mobile device security, vulnerability management, patch management, access & audit, awareness, physical security, personnel security, acceptable use, third party management, disaster recovery, data protection and secure data management. Policies are reviewed annually.
Risk Management
boberdoo conducts formal information security risk assessments annually and as necessary when system or application changes result in changes to our risk exposure. The risk assessment evaluates the current threat landscape and identifies information security risks in our environment and their potential impact to our business and customer data. Findings are discussed with stakeholders and we formulate a strategy and plans for risk treatment based on the assessment outcomes, risks identified and external compliance requirements.
Trusted Security Partners
Trek10
boberdoo partners with external service providers to enhance and support our security program. We have retained a certified AWS partner, Trek10, to monitor our infrastructure 24/7 for system availability, performance and security compliance.
Nationally Recognized Security Firms
We work with nationally recognized security services firms to conduct vulnerability assessments, penetration testing and web application testing annually.
SecurityMetrics
In addition to our annual tests and regular internal scanning, quarterly compliance scanning is conducted by SecurityMetrics to support us in best practices and compliance mandates.
Amazon Web Services Infrastructure
All systems are developed and hosted on Amazon Web Services' SOC 2 & ISO 27001 compliant infrastructure.
PROTECT
Security Awareness Training
Security awareness is a foundational aspect of the boberdoo security program. Awareness training is delivered to all employees annually and when first onboarded to the company. Continuous awareness is also provided via a variety of communications channels throughout the year. Employees are required to complete a training acknowledgment and test to validate their understanding of common security and privacy-related topics.
Network Protection
boberdoo systems are built for the cloud. Our platform is hosted on Amazon Web Services (AWS). As such, clients benefit from the many certifications achieved by AWS. To learn more, please visit the AWS Compliance Program site for information on applicable certifications. Our infrastructure is developed and deployed according to best practices and monitored for compliance with CIS-AWS benchmarks. Furthermore, our infrastructure is monitored and supported by a leading AWS-managed security services partner to add an additional layer of oversight and assurance.
Technical Security Controls
boberdoo's web application firewall protects your data against common web attacks including the OWASP Top 10. We monitor for malicious activity using intrusion detection systems and have capabilities for DDoS prevention to ensure the high availability of systems. Other security controls include:
• Logical access controls
• Encryption of data in transit (TLS/SSL)
• Encryption of data at rest
• Multi-factor authentication
• Review of third-party supplier security practices
• Access reviews and audits
• Continuous system patching and application updates
• Disaster recovery planning and testing
Access Management
All access at boberdoo must be requested, approved and authorized according to a user's roles & responsibilities and we adhere to the principle of least privilege. Passwords, access keys and role-based authentication mechanisms are used to authenticate users and services. Multi-factor authentication is required to access infrastructure systems. Access is promptly removed when a user is terminated and adjusted based on changing roles & responsibilities. All access and privileged actions are monitored and logged.
DETECT
Vulnerability Management
boberdoo contracts with external vendors to conduct vulnerability scanning and penetration testing annually. Industry-standard tools are used to identify and analyze vulnerabilities, audit system configurations and monitor compliance. Internal vulnerability scanning of critical infrastructure is performed on a monthly basis and integrated with our development process. Vulnerabilities are logged and remediated according to severity. It is our goal to never release a system update with a critical vulnerability and to promptly fix vulnerabilities when they are identified in existing systems.
- External vulnerability scanning and penetration testing annually
- Internal scanning monthly, integrated with development process
- Vulnerabilities logged and remediated by severity
Logging and Monitoring
boberdoo maintains a robust centralized logging environment. Logging is enabled in order to establish an audit trail for all system access. Logging is performed at the application level as well. Audit trails are implemented and secured to prevent unauthorized access. All infrastructure is monitored in real-time and alerts on availability, performance and security-related anomalies. Logs are retained for at least 12 months.
- Centralized logging environment
- Audit trail for all system access
- Real-time monitoring with alerts
- Logs retained for at least 12 months
RESPOND
Incident Response
boberdoo maintains an incident response policy and procedures to ensure security events are promptly identified, investigated, contained, remediated, and reported internally and externally, as necessary when customer and regulatory notifications are required. Our process defines roles & responsibilities, the severity of the incident, notification procedures, and remediation steps. All security events are logged and assessed upon identification. In the event of an incident, we will notify impacted customers in a timely manner of any security incident or breach that impacts your data. To report a security incident, please contact security@boberdoo.com.
RECOVER
Disaster Recovery
Data is replicated to multiple availability zones to support the high availability of systems and data. Critical business applications and systems are recoverable via failover to alternate regions in the event of a disaster. Disaster recovery procedures are documented and tested.
- Data replicated to multiple availability zones
- Critical applications recoverable via failover to alternate regions
- DR procedures documented and tested
Lead System Security Features
boberdoo has developed a lead system security and data management suite that allows you to build and implement a complete automated data security and retention strategy. Lead system security features include:
Two-Factor Authentication
Two-factor authentication set at the user level for logins to the boberdoo system
Sensitive Data Encryption
Sensitive data encryption with access via Secure Mode
Field Cleanup & Lead Deletion Rules
Individual field cleanup and full lead deletion rules
Automated Bulk Secure Export
Automated and bulk secure export to store encrypted data in your Amazon Web Services account
Real-Time PII Field Cleanup
Real-Time PII Field Cleanup
Real-Time Email & Phone Hashing
Real-Time Email & Phone Hashing
365 Day Lead Deletion
Maximum Retention Policy
365 Day Lead Deletion (maximum allowed retention). boberdoo enables and encourages clients to implement robust data retention and deletion policies because we believe that lead companies should retain data only as long as required to provide the requested service to consenting consumers - not forever.
Learn More About Lead System Security
Explore the full range of security features built into the boberdoo lead distribution system.
Questions About Security?
Our security team is available to answer your questions and support your vendor review process. Contact security@boberdoo.com.


