Another year, another laundry list of damaging data breaches due to flaws in data security plans. Sadly, the numbers and totals in damages continue to go up every year. Sure, massive companies like Equifax and Uber, which were among the biggest cyber attack victims of 2017, will certainly recover from their data breaches. However, most lead generation companies are not in the same position.
For lead generation companies, customer information isn’t just a useful tool for tracking purchases and preferences like it is for many businesses. Customer information is the product or service itself. For that reason, lead companies need to make data security a top priority for the good of the customers and for the sake of their businesses and the lead industry itself.
In this post, we touch on several important lead system features to consider when building your much-needed data security strategy.
1. Lead system Access
When it comes to data security, the first touchpoint you should consider is access to your lead distribution system. When it comes to lead system access, you should consider two options.
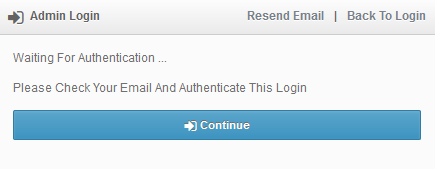
Login Authentication: Obviously, lead system users are required to enter their username and password upon every login attempt, but you may want additional security. For these cases, two-factor-authentication will require an additional email verification before the user can access the system.
User Group Control: As the administrator of your lead system, you can also set up user-based permissions to control exactly which features each user can access.
2. Data Views and Storage
Once a user is logged into your lead distribution system and navigating features they have access to, you can further secure your data by limiting or altering specific lead details.
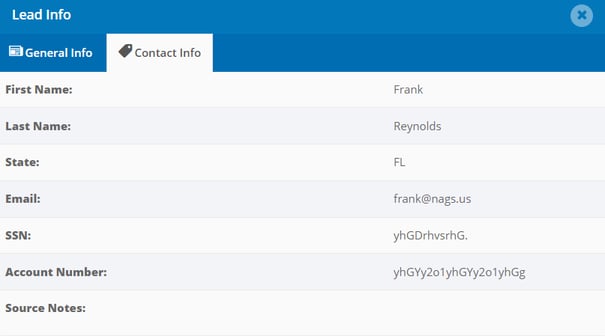
Sensitive Fields: You can mark any lead type field as sensitive to encrypt the value. The only way this value can be viewed is in Secure Mode, which logs all user activity and records the specific leads and fields that were accessed. Furthermore, Secure Mode can be enabled at the user level, leaving the option to never allow specific users the ability to see sensitive fields.
PII Fields: Coming soon, you will be able to mark personally identifiable contact fields for any lead type which will mask the true value of the field with asterisks “*****”. These fields cannot be decrypted, which makes this method the most secure way to retain personally identifiable contact fields.
3. Data Deletion
While the data view features listed above give you good options to secure the data you retain in your system, the single best way to keep your lead business safe is to delete the fields or leads the second you no longer need them.
Field-Level Deletion: You can mark any lead type field as a cleanup field and specify the number of hours or days you want to keep the field in your lead system before deleting it entirely.
Lead-Level Deletion: The same logic goes for lead-level deletion. In this case, instead of deleting a single field, you remove the entire lead from your lead system and database.
4. Data Retention
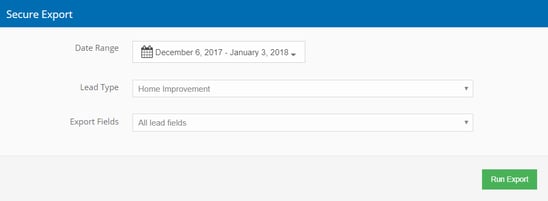
Before encrypting or deleting any specific leads or lead fields, some lead companies need to retain specific pieces of data. For these scenarios, we have built a secure export option that allows you to retain specific data.
Amazon S3 Secure Export: This feature allows you to automatically or manually export the leads of your choice, which are then securely stored in your Amazon S3 account.
Each of the features mentioned above were developed by boberdoo to help our clients keep their customer data safe. We highly recommend taking a close look at your business and building an airtight data security policy. With these tools, you can do just that.



